Table Of Contents

Introduction
Similar to my post PnP PowerShell - MFA account and Client Id from a while back, I wanted to document how to use your own application registration with Microsoft Graph PowerShell. My friend wanted to be able to read Cloud PCs (such as Windows 365) with a custom application registration using Microsoft Graph.
So, in this post, we will first look briefly at what Microsoft Graph PowerShell is. Then create a custom application registration and configure it to work with the Graph PowerShell module to retrieve cloud PC data.
NOTE: Microsoft Graph PowerShell 2 is out in public preview. There are many upsides to the new module. Read more here Microsoft Graph PowerShell v2 is now in public preview, half the size and speeds up automation - Microsoft 365 Developer Blog
Microsoft Graph PowerShell
The Microsoft Graph PowerShell SDK is open source PowerShell module that gives you access to all Microsoft Graph APIs while using modern authentication via MSAL. It works with Windows PowerShell 5.1 and has cross-platform compatibility via PowerShell 7 and later.
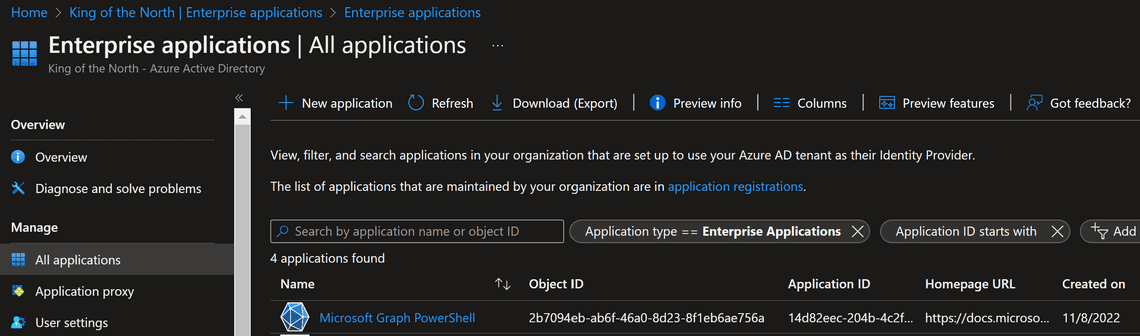
To make it easier for the consumers of this module, they use an multi-tenant app as default. Suppose you, as an admin, consent and allow people in your organization to use Microsoft Graph PowerShell, the app is added to enterprise applications in the Azure AD of your tenant.
You can use this default app registration or a custom one.
TIP: If you are new to the Microsoft Graph PowerShell SDK, I recommend you to read about it here Microsoft Graph PowerShell overview
Make sure to install it. And also, read the documentation on how to use it: Install the Microsoft Graph PowerShell SDK Get started with the Microsoft Graph PowerShell SDK
Custom Application Registration
Let’s create a custom Azure AD application registration that uses delegated permissions - similar to the Microsoft Graph PowerShell app.
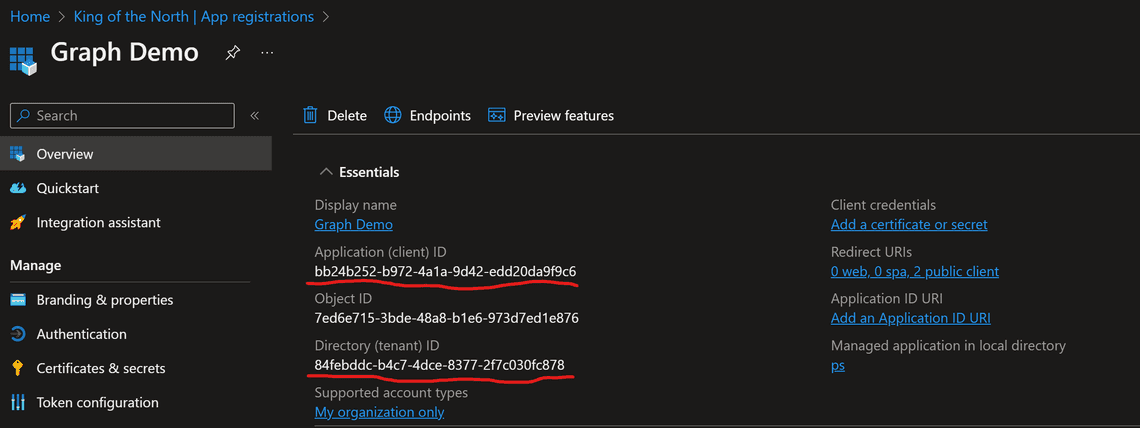
After you create the new application, note the Application Id and Tenant Id, as we will use them later.
NOTE: read more here if you are new to registering Azure AD apps: register-application
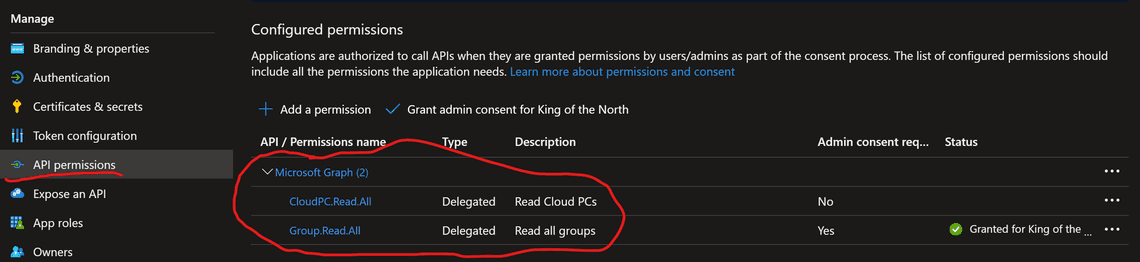
Configure the required permissions
In this case, I’m using the delegated permissions CloudPC.Read.All (the one my friend wanted), and Group.Read.All. The latter is used to show you that everything works since I currently have no Cloud PCs in my demo environment.
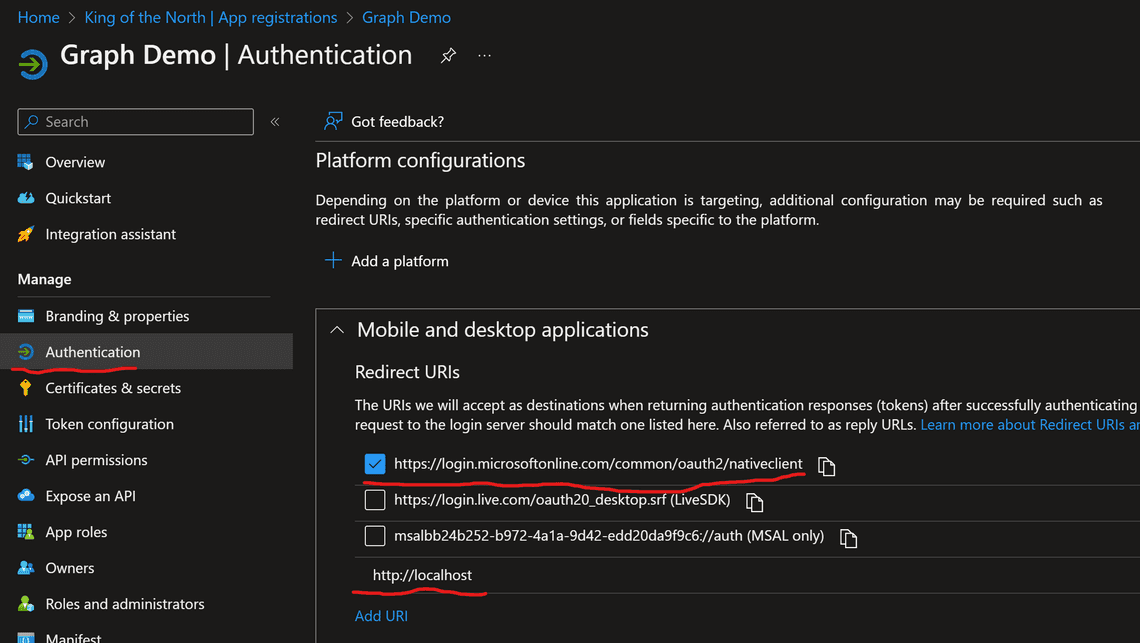
Reply-URLs
We need reply URLs to receive the access tokens from Azure AD. To ensure versatility, I usually add support for both PowerShell 5.1 and PowerShell 7.1 and forward.
- PowerShell 5.1: select https://login.microsoftonline.com/common/oauth2/nativeclient
- PowerShell 7.1: add http://localhost
Connecting and getting results
If we were using the default experience, you would just connect with the requested scope:
Connect-MgGraph -Scopes "CloudPC.Read.All"
Using the setup with a custom app registration, we provide the previously noted Application Id and Tenant Id:
Connect-MgGraph -Scopes "CloudPC.Read.All" -ClientId "bb24b252-b972-4a1a-9d42-edd20da9f9c6" -TenantId "84febddc-b4c7-4dce-8377-2f7c030fc878"
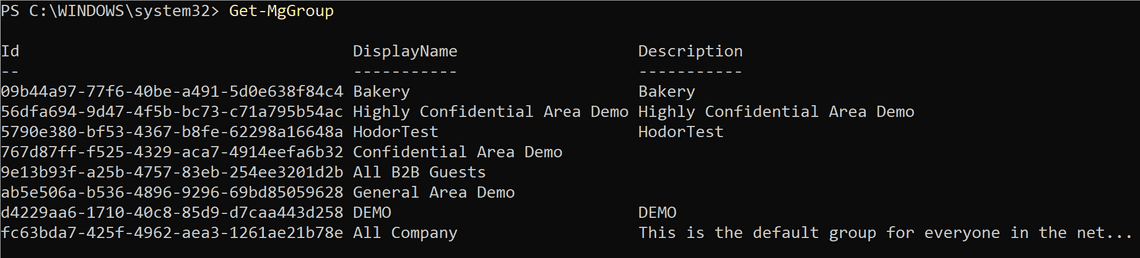
Retrieving something tangible
First, we connect using the Group.Read.All:
Connect-MgGraph -Scopes "Group.Read.All" -ClientId "bb24b252-b972-4a1a-9d42-edd20da9f9c6" -TenantId "84febddc-b4c7-4dce-8377-2f7c030fc878"
Then retrieve the Microsoft 365 Groups:
Get-MgGroup
That’s all, folks
Just a quick and dirty post, haha.
Thank you for reading
/Simon
Related Posts